Common Scams and Frauds – How to Avoid Them4 min read
March 29, 2019These days, it seems like everyone’s out to take your money and various bad actors have plenty of ways to do so. Below are three of the ones we’ve seen recently ourselves and with our customers.
Blackmail
The emails are from the address they’re sent to, and the emails all seem to have mostly the same form: “Hi, your account is infected!” the email reads. “You probably do not know anything about me and you are most likely wondering why you’re receiving this electronic message, proper?” Clearly we’re dealing with a native English speaker. “I’mhacker who openedyour emailand OStwo months ago [sic].” I find that highly unlikely. “Do not attempt to msg me or find me, it’s not possible, considering that I directed you an email from YOUR hacked account.”
Perhaps you’ve seen an email like this? The email goes on to say that they’ve keylogged everything you type, accessed your screen, and your webcam (this line is really funny to us since none of us have webcams on our computers). The email threatens to expose your secrets and online activity (specifically naming the adult variety) to your contact list unless you pay them an exorbitant amount of money via bitcoin and giving you 48 hours to do so.
As you might suspect, this email is indeed preposterous, both technically, as well as realistically. But then how did they send the email from your account? In truth, they didn’t. Sending an email from any address real or contrived is trivially simple. One need only use an email server that doesn’t require authentication to send messages and send them with a fake return address. As for the contents they’re entirely contrived. They’re worded in such a way (likely including spelling mistakes) to make the recipient believe that the sender is some elite hacker. One can see that the email doesn’t come from where it purports to when checking what are called the headers. This is basically like a postmark that servers which send or relay the message put on the message to indicate its path to your inbox.
Fake Bills
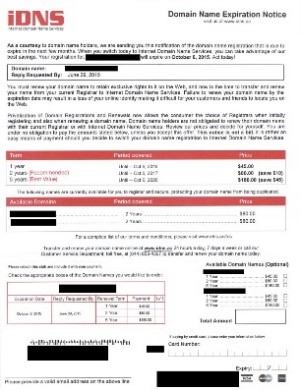
Blackmail isn’t the only scam we’ve seen. Some of our customers have received Domain Renewal bills from a company called iDNS. iDNS, while legitimate in the sense of being able to renew and register domain names, does not send legitimate notices of this kind. A picture of the letter they send can be seen here:
None of Sharp Innovations’ clients have their domain name registered through iDNS and for good reason: they charge 4-6 times greater than the market rate for Domain Name services. Also they employ shady tactics like those found in this letter formatted intentionally to look like a bill or invoice. Also notice that they cannot seem to get the domain name “idns.com” but instead have to use “idns.ac”. They intentionally send these letters more than three months before the expiration (which is when most registrars will send reminder emails that the domain is coming up for renewal).
Robocalls
Perhaps you’ve received a call where a recording tells you that you have not “verified your Google listing”. The recording explains that if you do not verify your Google listing, that anyone can make changes to your profile or even your site, and that if you press 1, you can be connected to your “local google specialist”. None of these calls are legitimate.
Google will not call you for any reason with a robocall unless you specifically request it. These companies hope to scam you into purchasing their services (much like iDNS does) at best, or defraud you at worst. If you receive such a robocall, we recommend you hang up.
If you are one of our clients and have fallen victim to any of these scams, take whatever action is necessary to get your money back and to complain to the FTC about the scam. You can reach their complaint form here: www.ftccomplaintassistant.gov.